UNREVEALED FILES ™ on Twitter: "Hardware Trojans are becoming increasingly common and concerning in recent years due to growing numbers of attacks such as data theft and backdoor insertions into the electronics
Forschung im Kampf gegen Cyberangriffe durch Hardware-Trojaner | EPoCH Project | Results in brief | H2020 | CORDIS | European Commission

A machine-learning-based hardware-Trojan detection approach for chips in the Internet of Things - Chen Dong, Jinghui Chen, Wenzhong Guo, Jian Zou, 2019
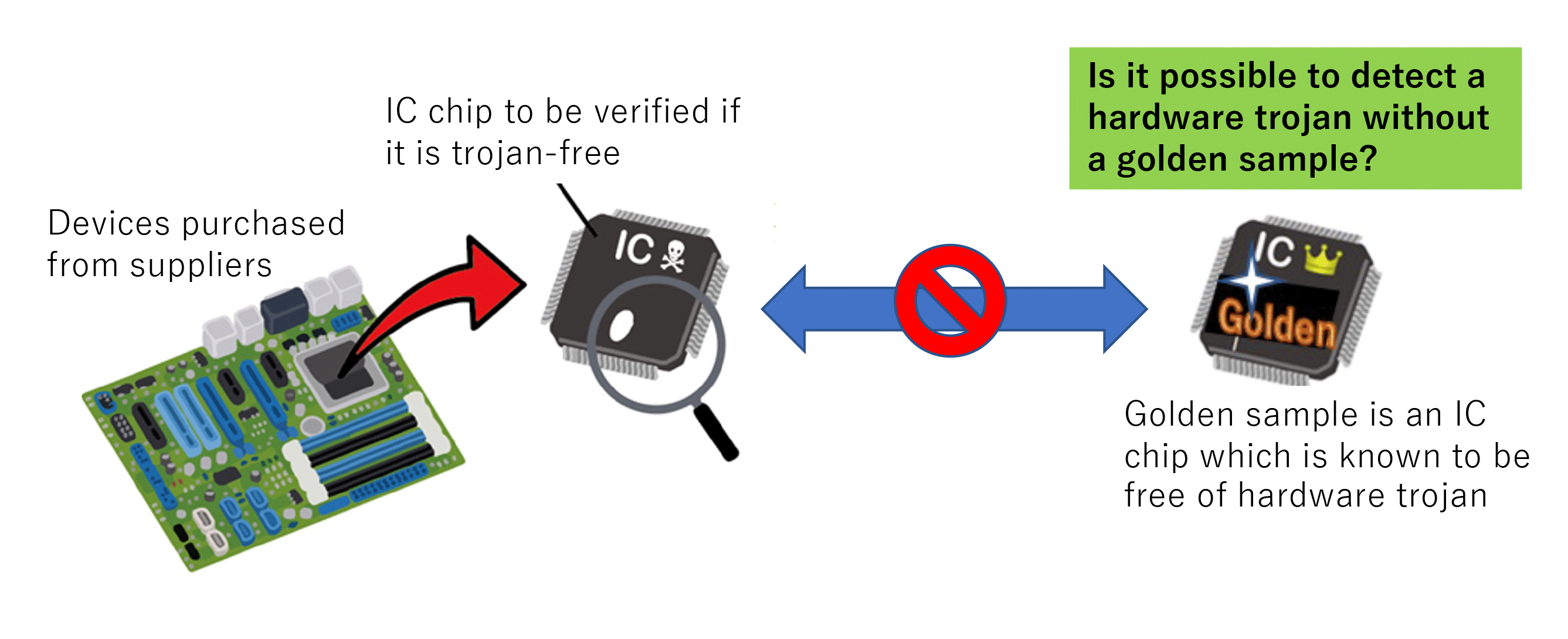
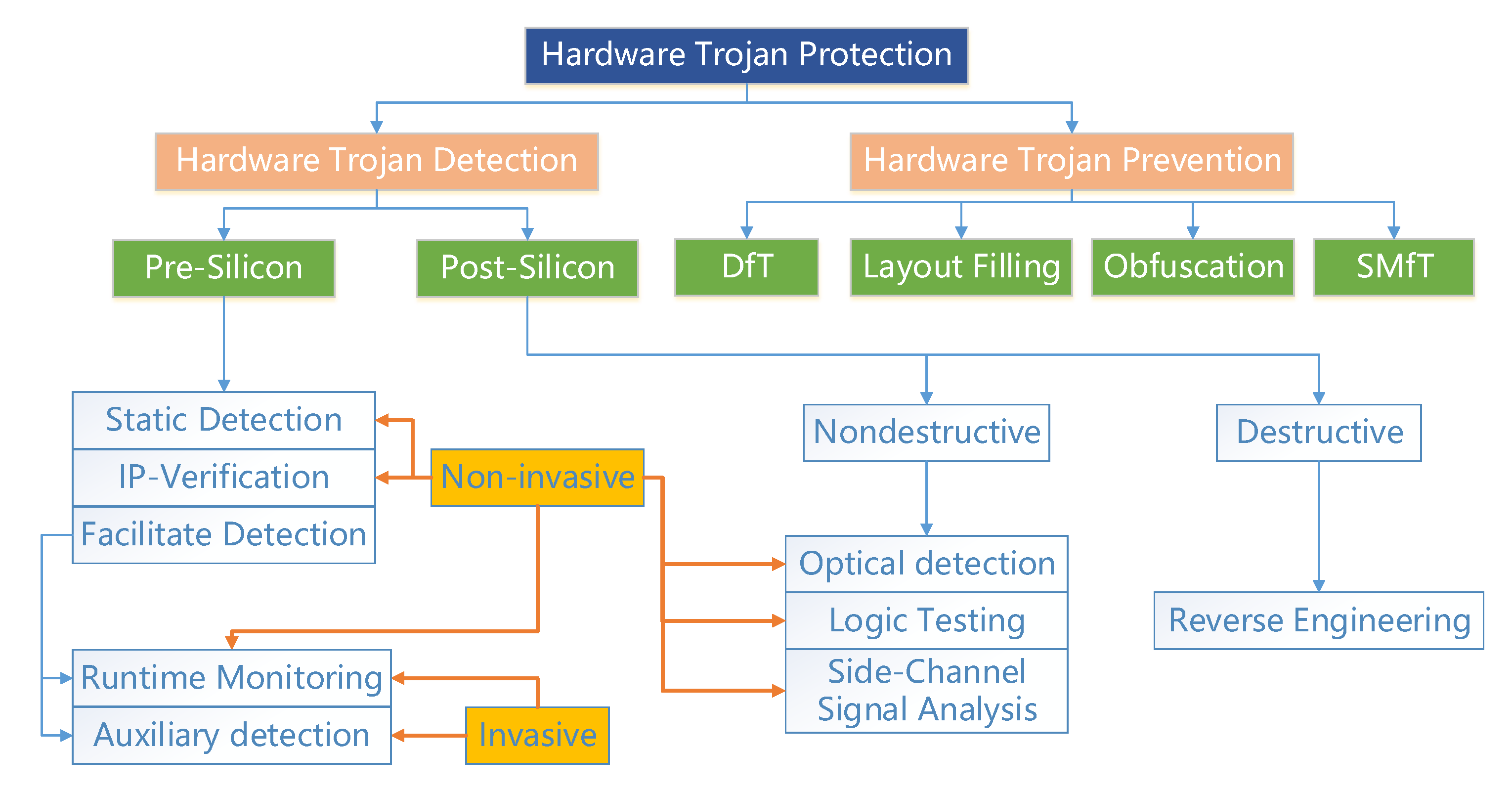
Research on hardware Trojan - Research | Hardware security research team | Cyber physical security reserch cente



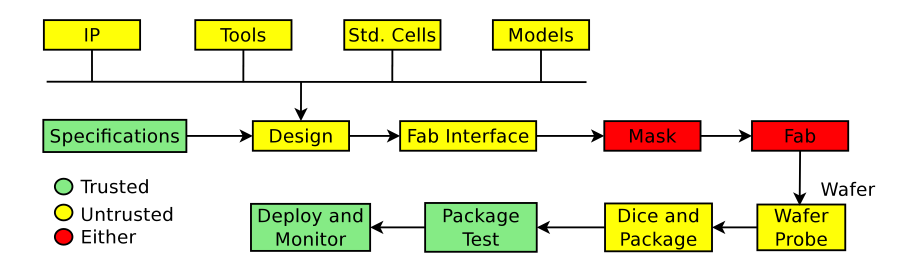
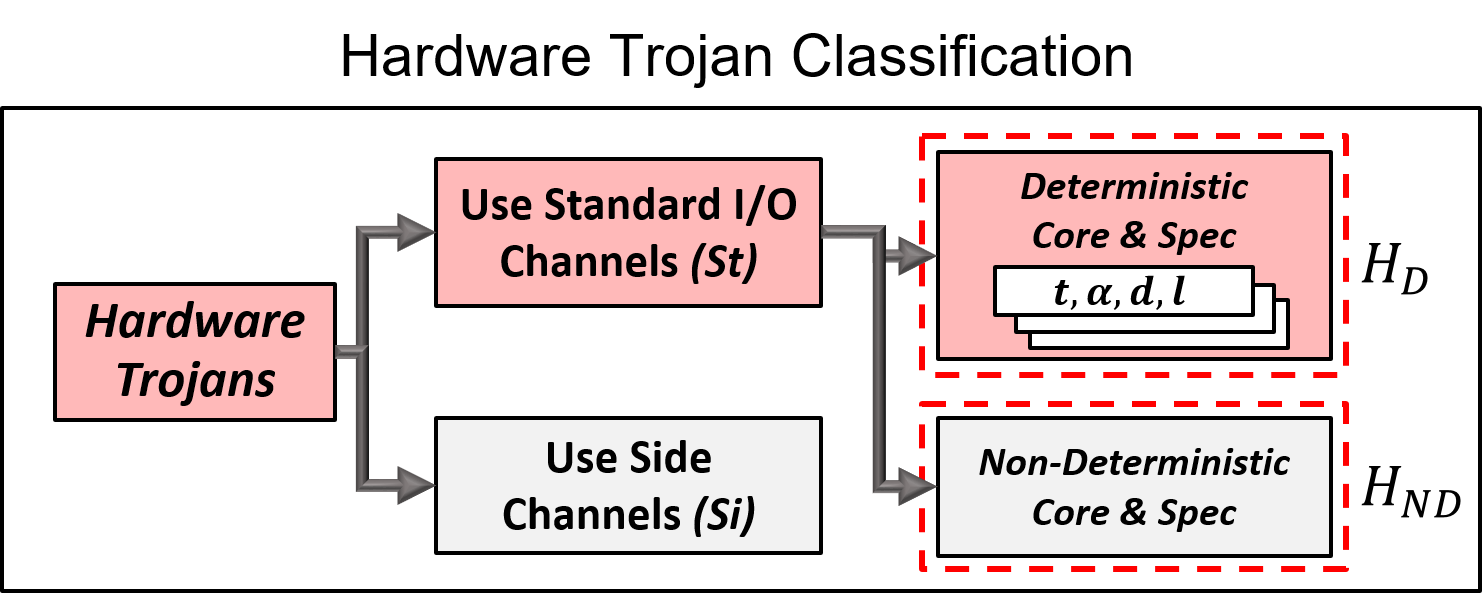







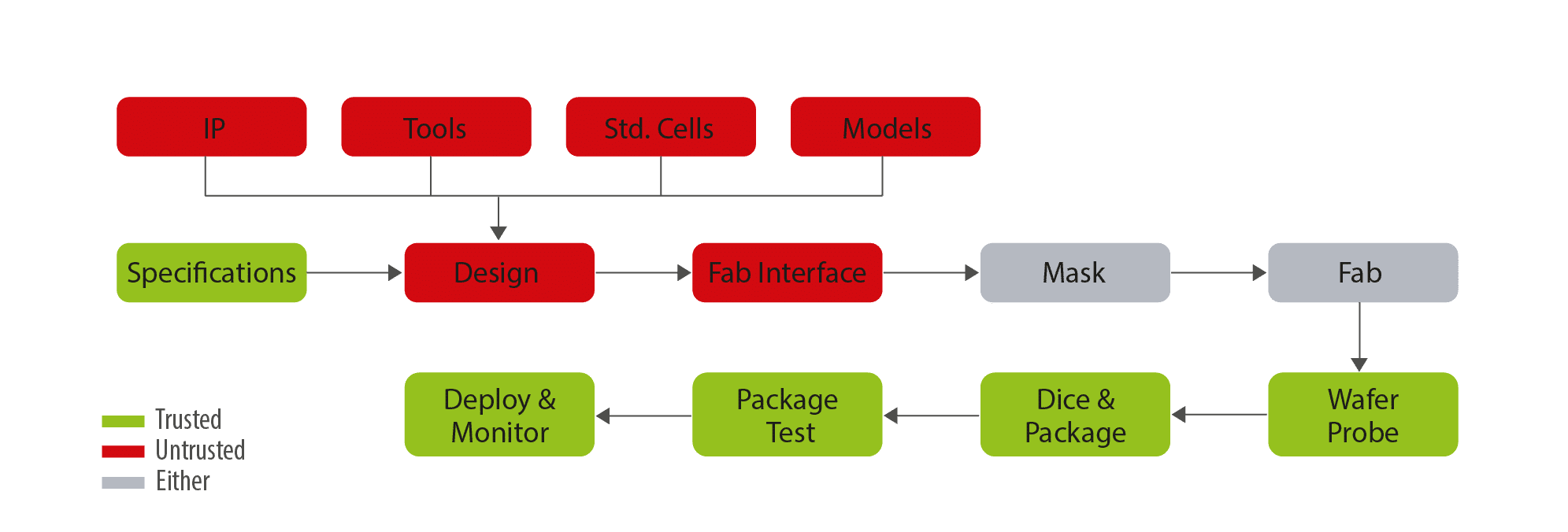
![PDF] Trustworthy Hardware: Identifying and Classifying Hardware Trojans | Semantic Scholar PDF] Trustworthy Hardware: Identifying and Classifying Hardware Trojans | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/4d9d3df6f23afef5605ae45b46deb30ffe13894f/3-Figure1-1.png)