The Hardware Trojan War: Attacks, Myths, and Defenses : Bhunia, Swarup, Tehranipoor, Mark M.: Amazon.de: Bücher

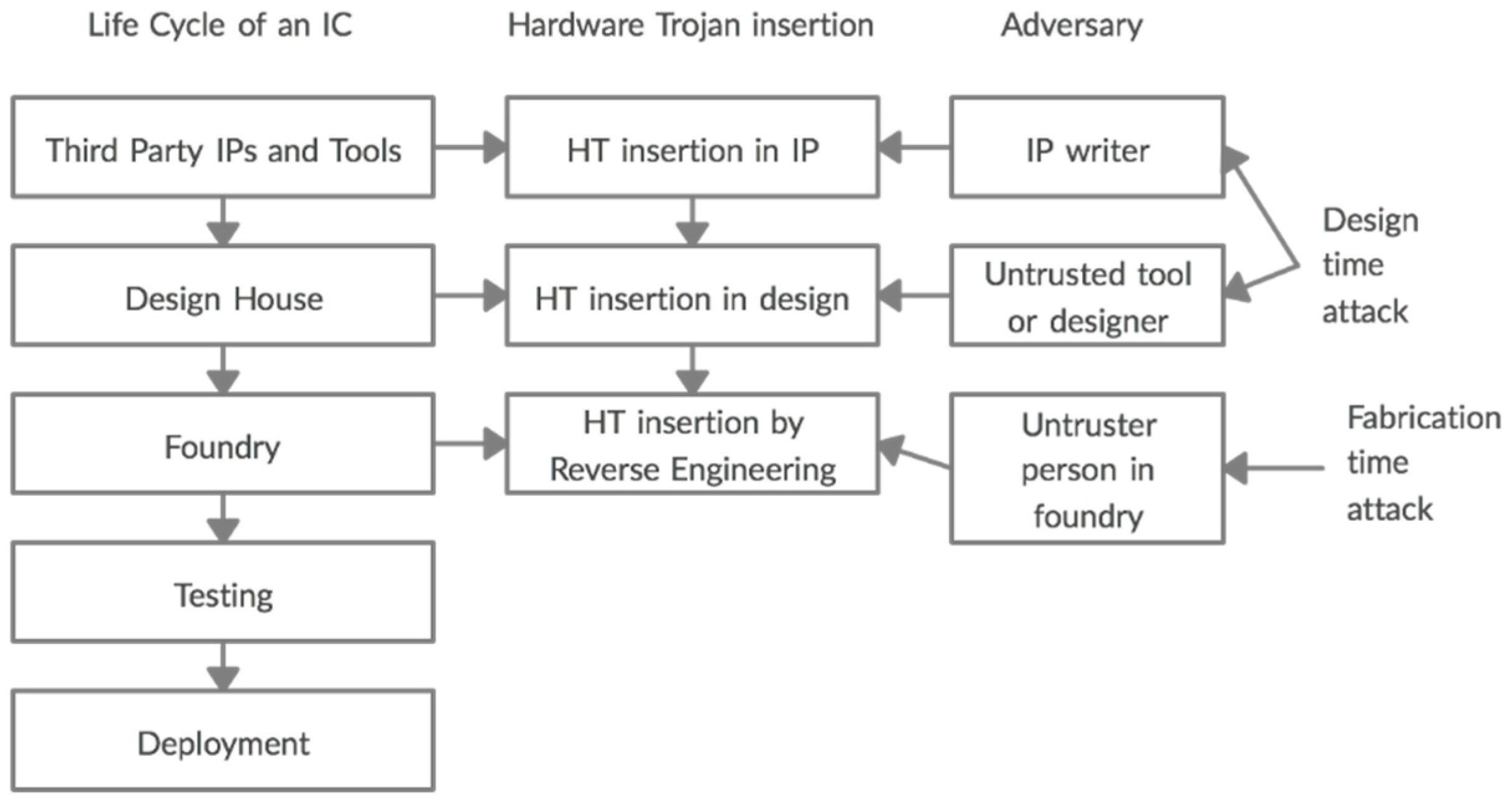
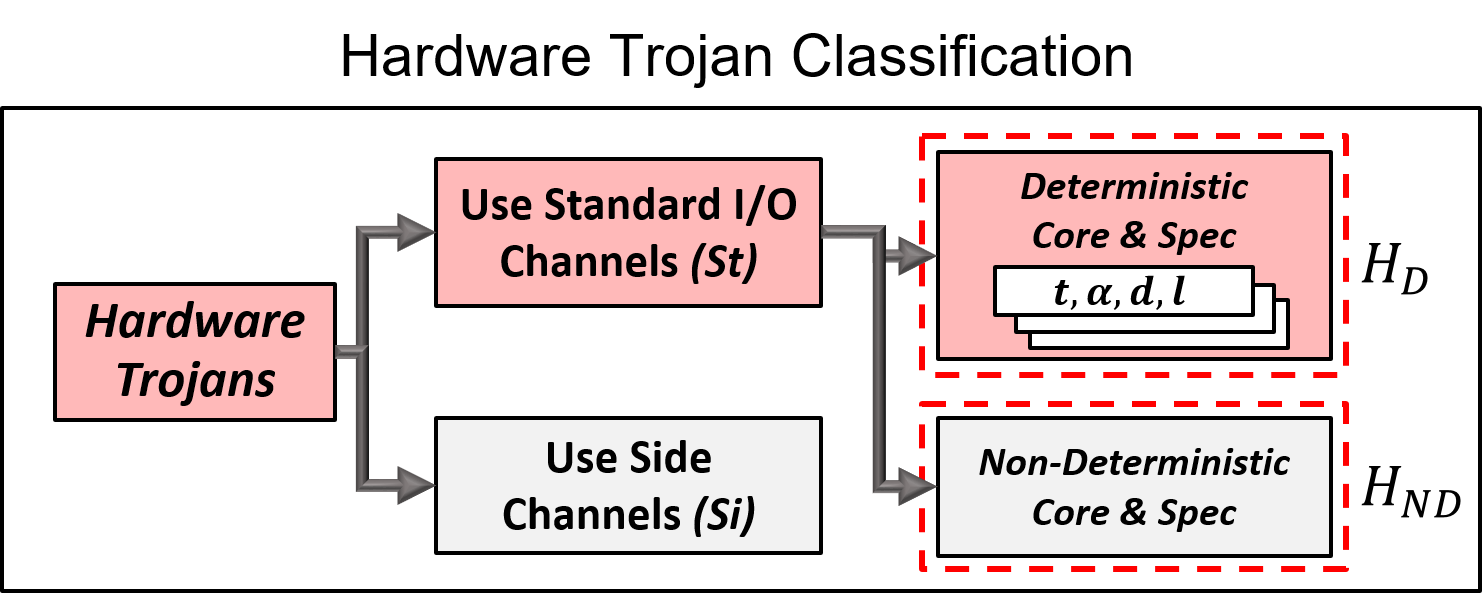
Ten years of hardware Trojans: a survey from the attacker's perspective - Xue - 2020 - IET Computers & Digital Techniques - Wiley Online Library

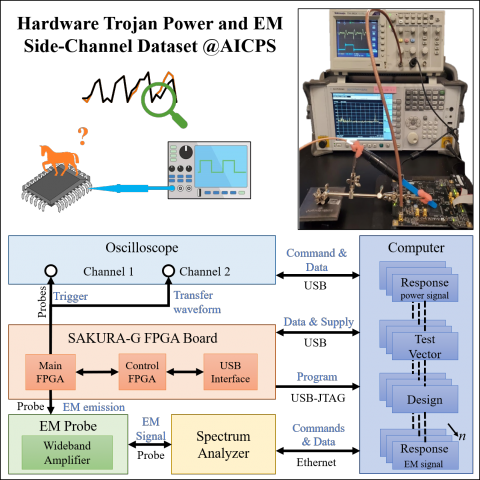
Runtime Identification of Hardware Trojans by Feature Analysis on Gate-Level Unstructured Data and Anomaly Detection

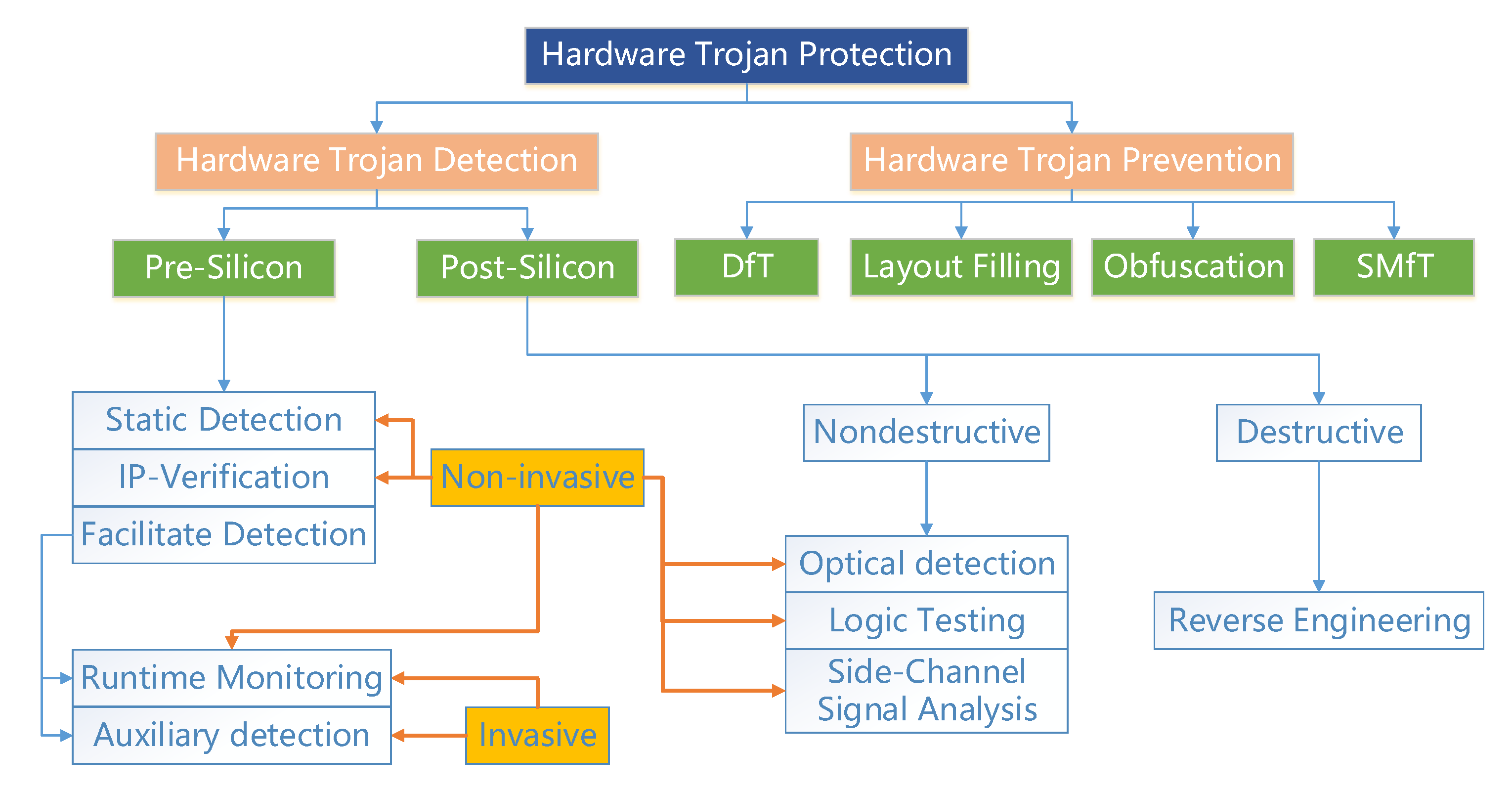
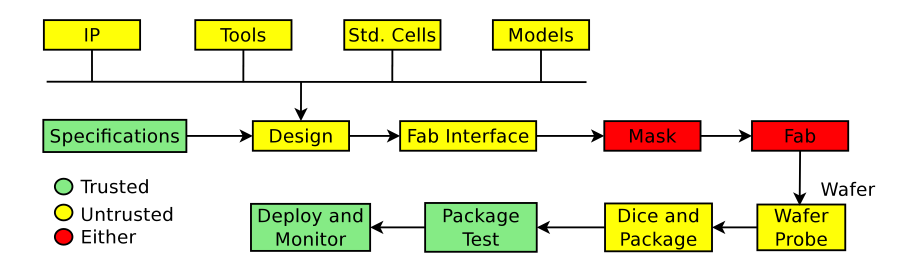
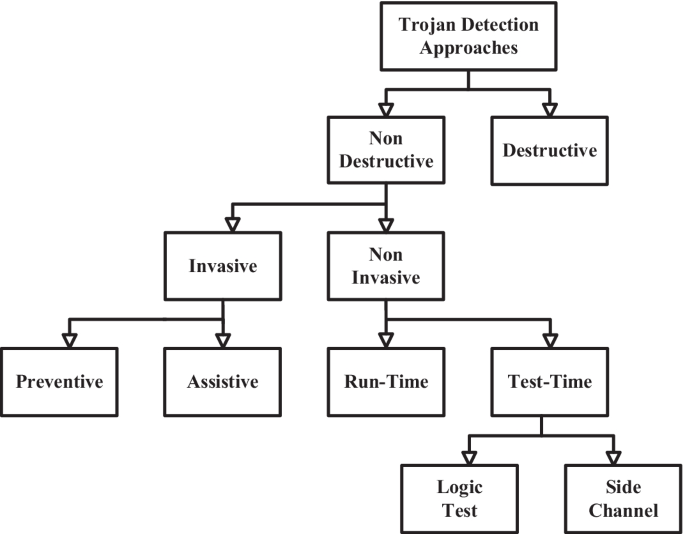
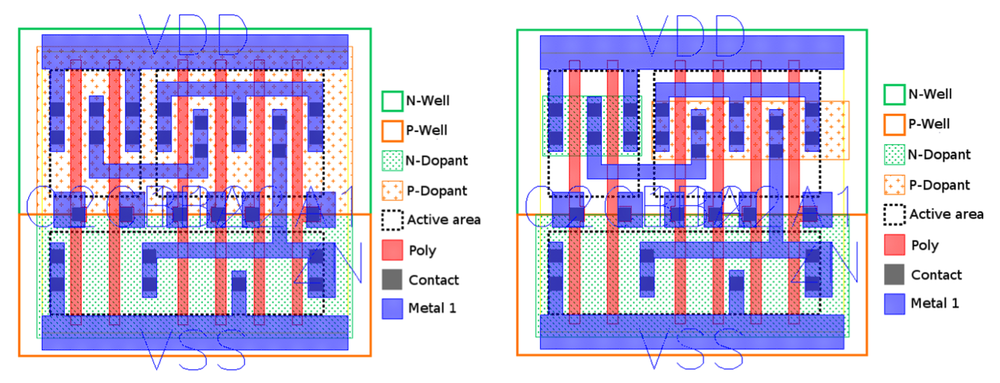
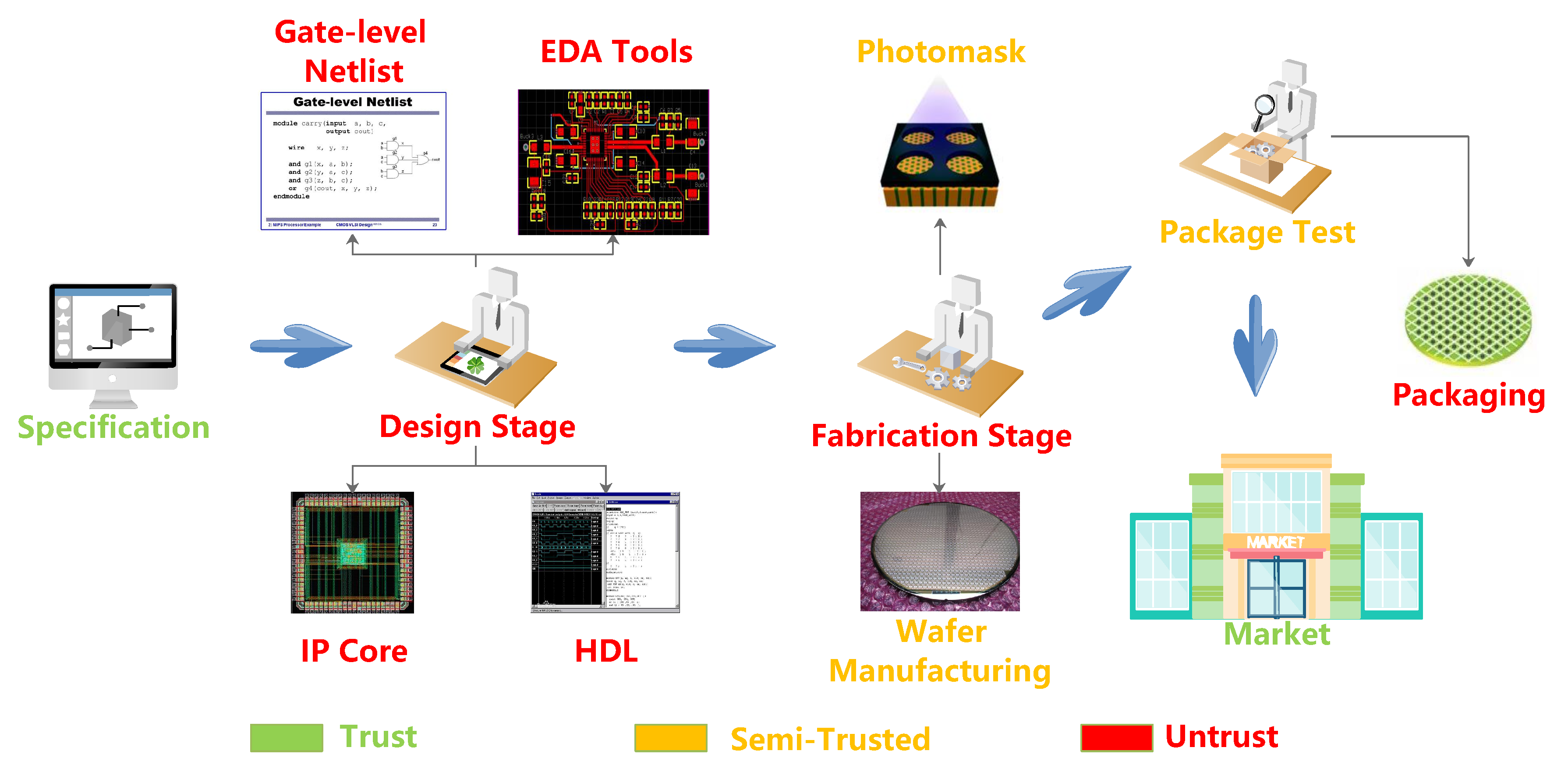
Conventional and machine learning approaches as countermeasures against hardware trojan attacks - ScienceDirect
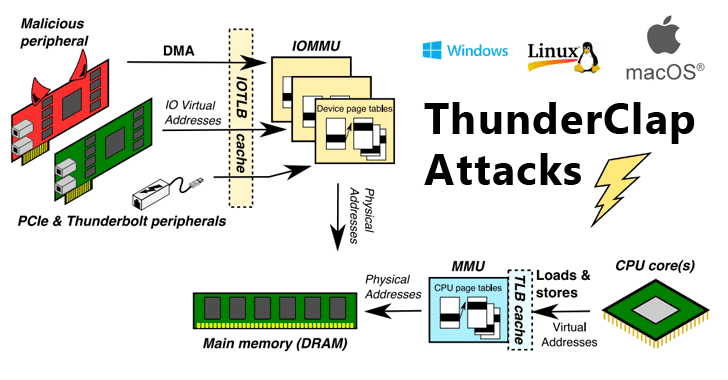
Understanding – and preventing – the malicious hardware Trojan | EPoCH Project | Results in brief | H2020 | CORDIS | European Commission

Conventional and machine learning approaches as countermeasures against hardware trojan attacks - ScienceDirect
A Stealthy Hardware Trojan Exploiting the Architectural Vulnerability of Deep Learning Architectures: Input Interception Attack
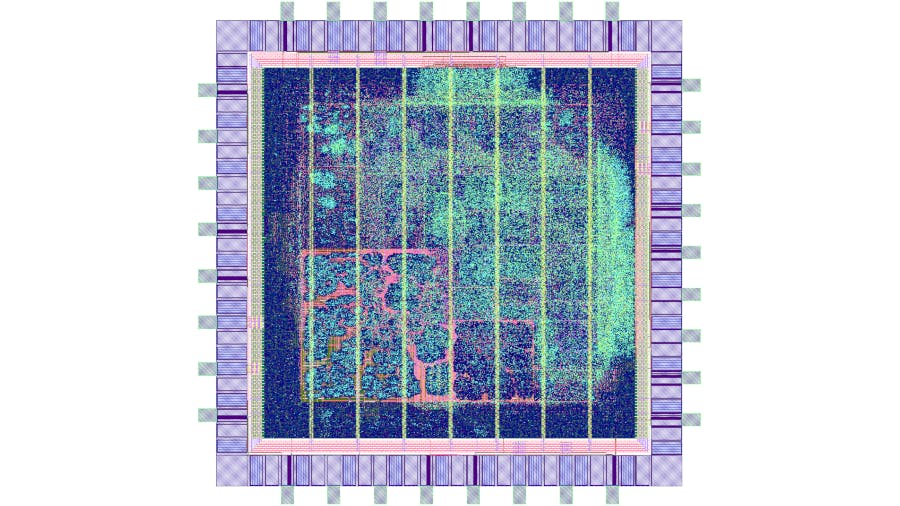
Researchers Spot Silicon-Level Hardware Trojans in Chips, Release Their Algorithm for All to Try - Hackster.io

![PDF] Hardware Trojan Attacks on Neural Networks | Semantic Scholar PDF] Hardware Trojan Attacks on Neural Networks | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/621227db6a9b0ad374cf737fea3760b49c4de42c/3-Figure2-1.png)