Applied Sciences | Free Full-Text | Classification and Analysis of Malicious Code Detection Techniques Based on the APT Attack
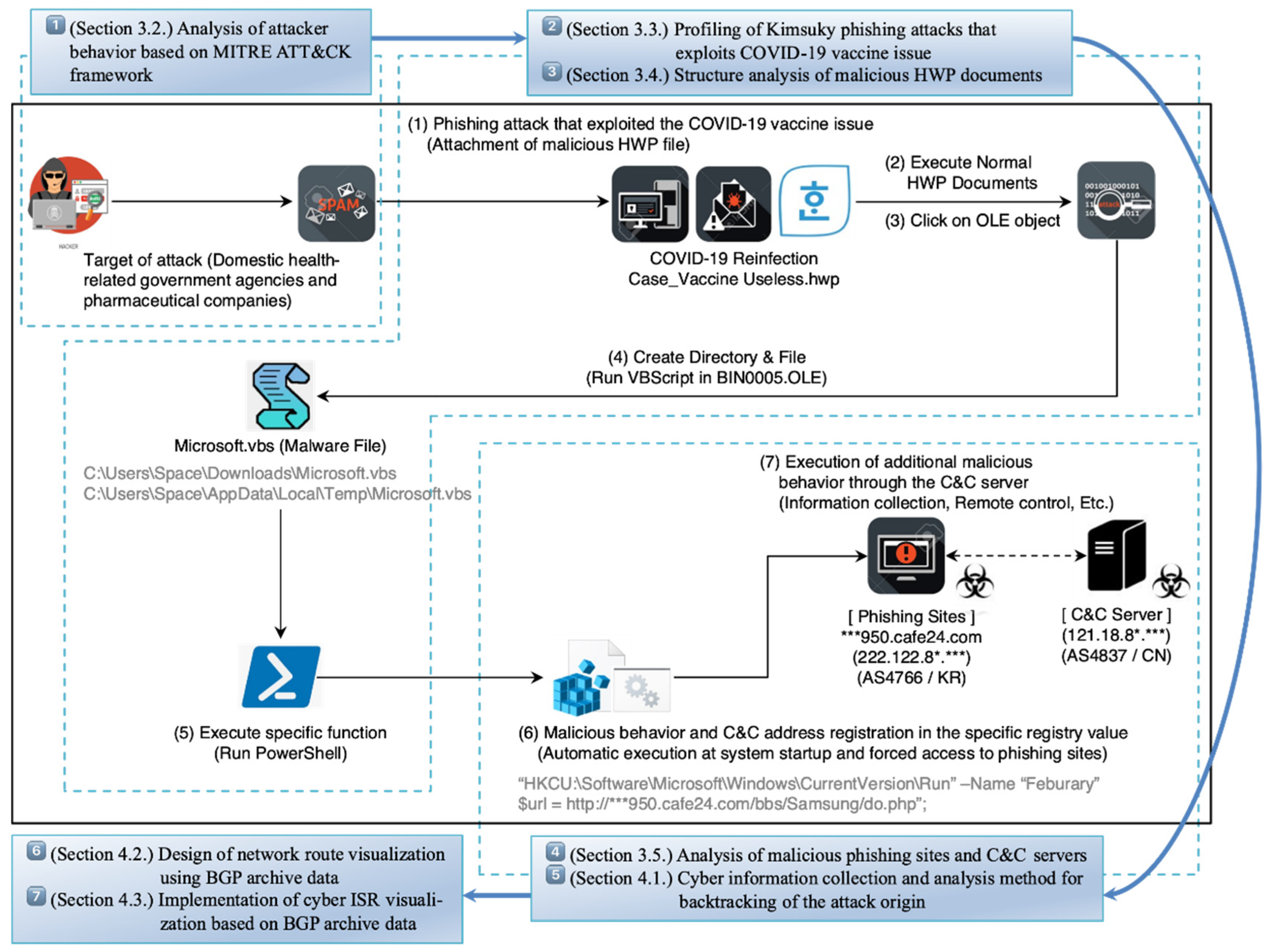
Electronics | Free Full-Text | Research on Cyber ISR Visualization Method Based on BGP Archive Data through Hacking Case Analysis of North Korean Cyber-Attack Groups
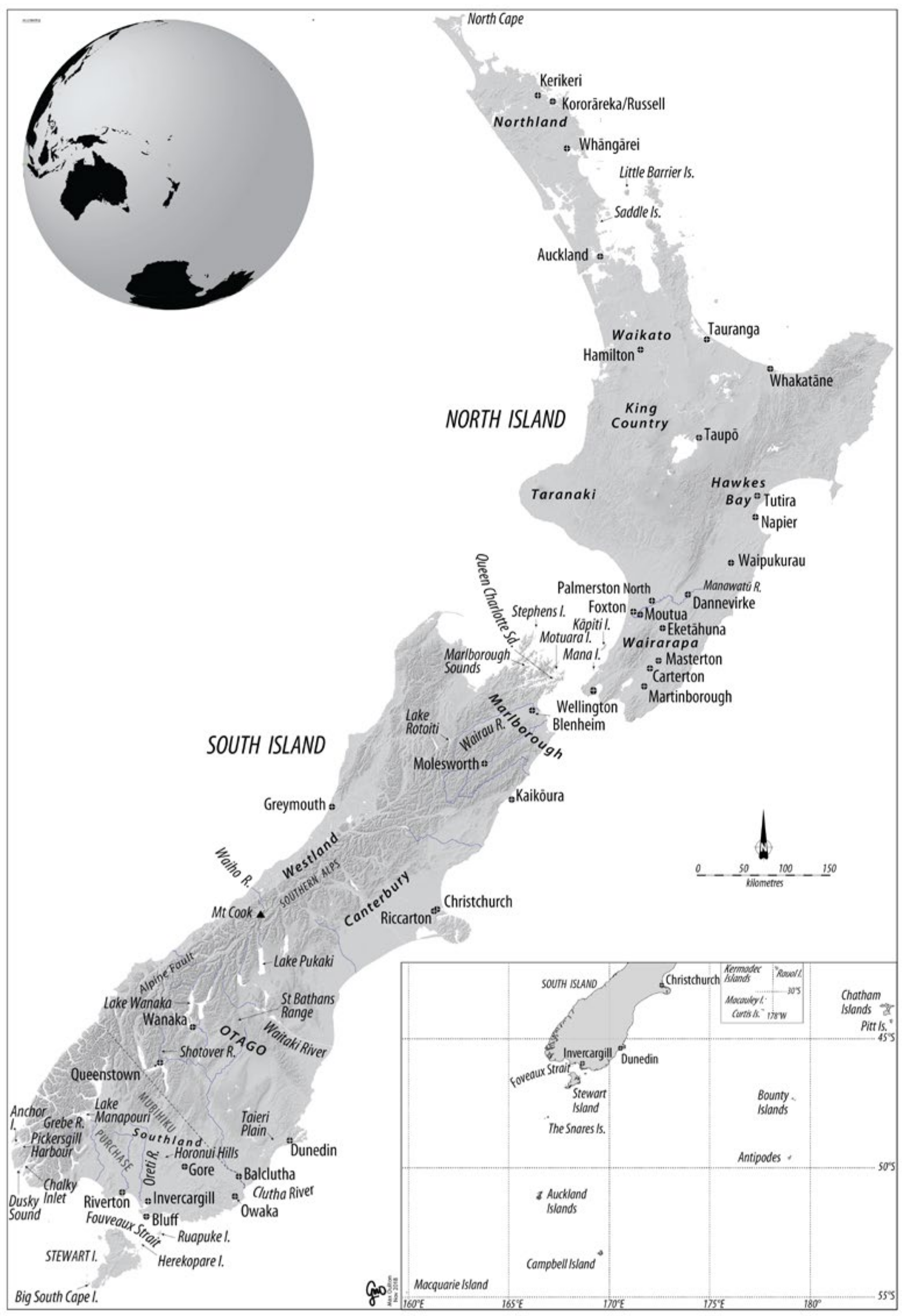
Life | Free Full-Text | Abundance and Dynamics of Small Mammals in New Zealand: Sequential Invasions into an Island Ecosystem Like No Other
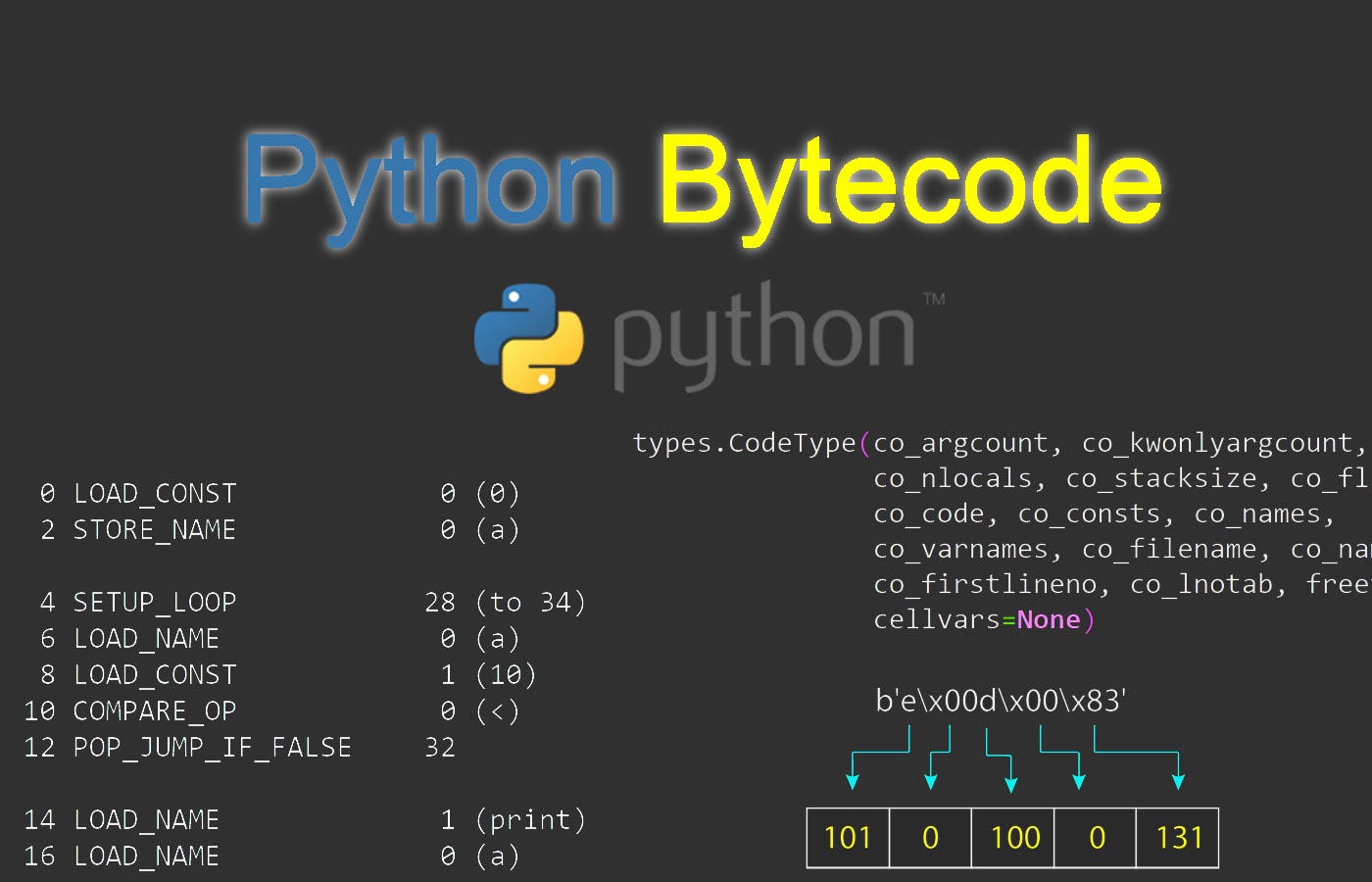
Understanding Python Bytecode. Learn about disassembling Python… | by Reza Bagheri | Towards Data Science
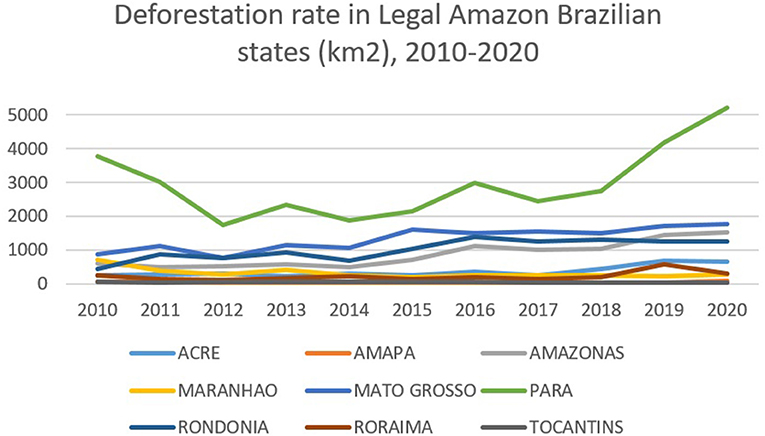
Frontiers | Framing Illegal Logging and Its Governance Responses in Brazil – A Structured Review of Diagnosis and Prognosis